A Chinese state-linked hacker group has claimed responsibility for infiltrating key offices of the Indian government, including the Prime Minister’s Office (PMO), as well as businesses like Reliance Industries Limited and Air India. This revelation comes to light through leaked data meticulously reviewed by India Today’s Open-Source Intelligence (OSINT) team.
The I-Soon Leak: What We Know
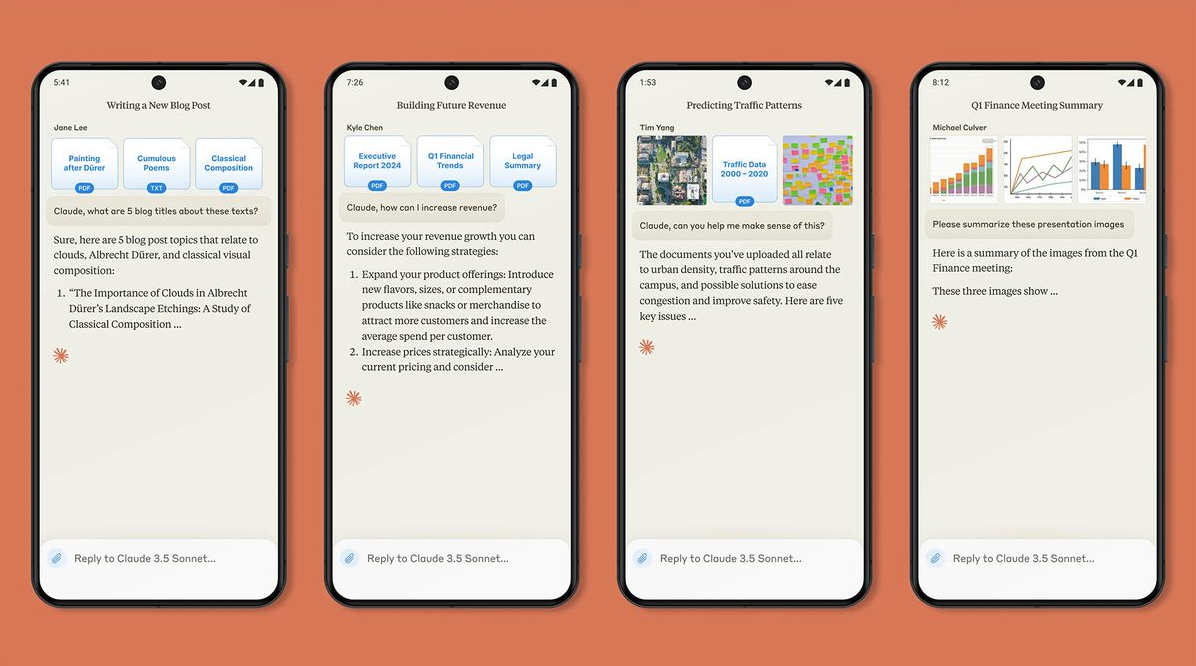
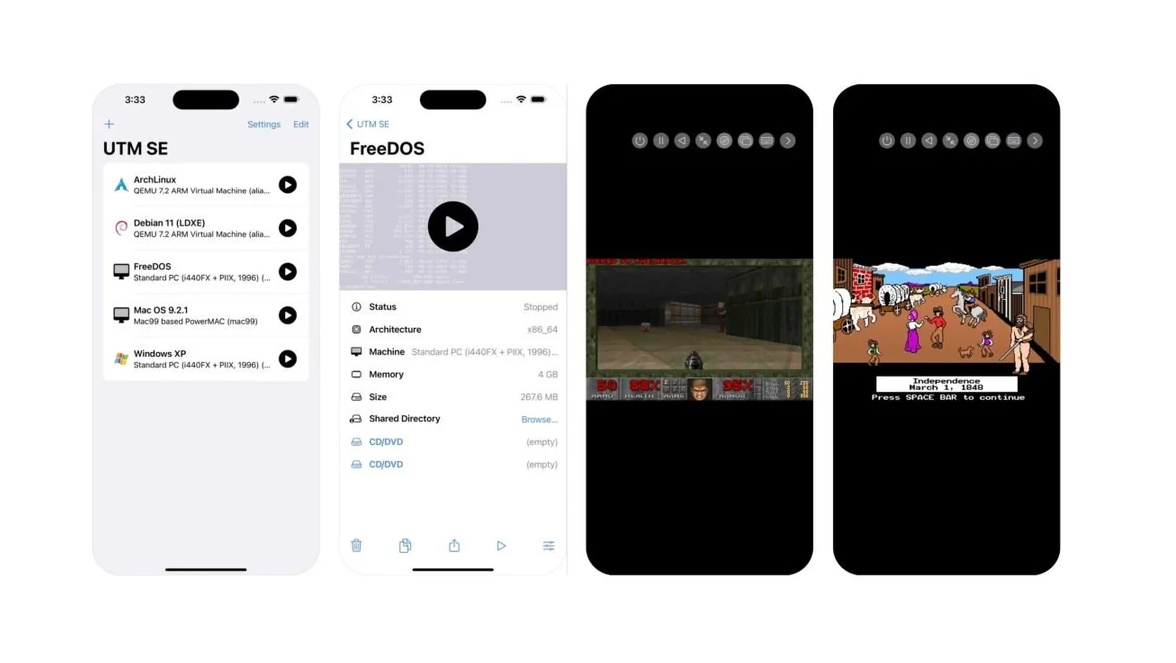
I-Soon, an alleged cybersecurity contractor associated with China’s Ministry of Public Security (MPS), finds itself at the center of this controversy. Thousands of documents, images, and chat messages linked to I-Soon were anonymously posted on the developer platform GitHub over the weekend.
GitHub, a collaborative space for developers working on open-source projects, became the unexpected conduit for this massive leak.
I-Soon, in conjunction with Chinese authorities, has launched an investigation to determine how these files were exposed. Employees of the contractor were informed that the leak would not significantly impact business operations and were advised to continue working as usual.
What is I-Soon?
I-Soon is a Shanghai-based company that reportedly provides cybersecurity services to the Chinese government, including the Ministry of Public Security, Ministry of State Security, and the People’s Liberation Army.
What was leaked through I-Soon?
Thousands of documents, images, and chat messages were posted anonymously on GitHub, a developer platform, on February 16th. The leaked data allegedly reveals details of I-Soon’s operations, including:
- Targets: The leak mentions Indian government offices, including the Prime Minister’s Office (PMO) and Home Ministry, as well as private entities like Reliance Industries Limited and Air India. Other targets include NATO, European governments, and even some Chinese allies like Pakistan.
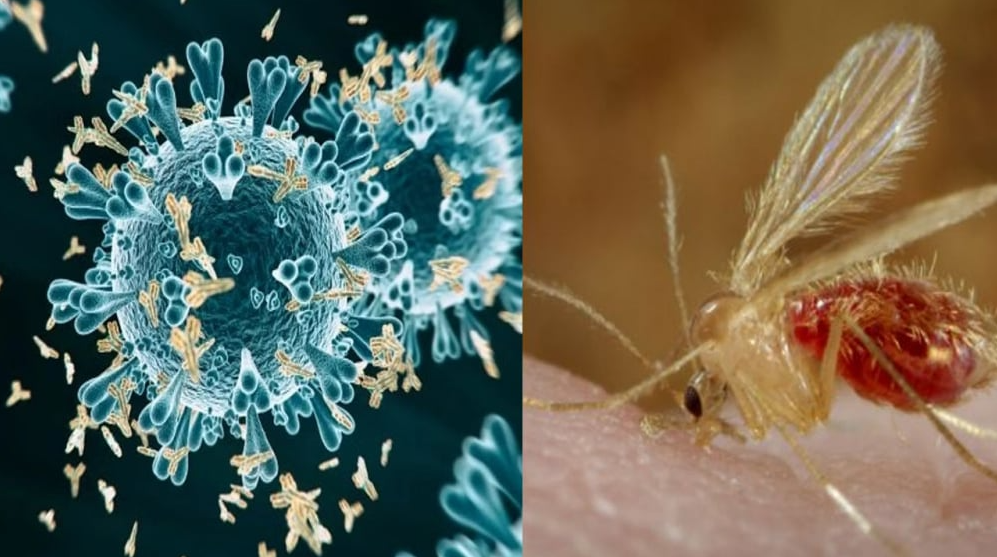
- Techniques: The leak describes malware, hacking tools, and techniques allegedly used by I-Soon, including a “poisoned” power bank that can upload data from victims’ machines.
- Internal Operations: The documents shed light on I-Soon’s bidding processes, contracts with government agencies, and internal discussions about hacking operations.
The Complex Web of Cyber Espionage
The leaked data sheds light on a sophisticated network of clandestine hacks, spyware operations, and extensive surveillance orchestrated by Chinese government-linked cyber threat actors. Here are some key points:
- Targets: The Chinese hacker group claimed to have targeted not only Indian government offices but also entities such as the North Atlantic Treaty Organisation (NATO), European governments, and private institutions. Even Beijing’s allies, including Pakistan, were not spared.
- Modus Operandi: Machine-translated internal documents, originally in Mandarin, reveal the attackers’ methods, preferred targets, and exploits. However, the leak does not provide direct samples of stolen data or specify the extent of penetration and duration of attacks on individual targets.
- Indian Targets: Among the Indian entities mentioned in the leak are the Ministry of Finance, the Ministry of External Affairs, and the Presidential Ministry of the Interior (likely referring to the Ministry of Home Affairs). During the height of India-China border tensions, advanced persistent threat (APT) groups accessed approximately 5.49GB of data related to various offices within the Presidential Ministry of the Interior between May 2021 and October 2021.
A Wake-Up Call for Cybersecurity
The I-Soon leak underscores the maturing nature of China’s cyber espionage ecosystem. As the world grapples with increasing cyber threats, governments and organizations must remain vigilant and strengthen their defenses against such attacks. The breach serves as a stark reminder that no institution is immune to the reach of determined hackers.
While investigations continue, the fallout from this leak will undoubtedly reverberate across international borders, prompting urgent discussions on cybersecurity protocols and cooperation.
Disclaimer: The information provided in this article is based on leaked data and ongoing investigations. It is subject to updates and further verification.